In the first nominating contests of the 2020 election, we have seen a pattern emerge that is potentially more insidious than many experts anticipated in the immediate aftermath of the 2016 election hacks. Even before cyber attacks and pandemics threatened our elections, infrastructure obstacles, like touch screen voting machines and staffing shortfalls, have a long history of causing hours long voting lines and omitting thousands of voter registration forms. COVID-19 will only make these staffing shortfalls and infrastructure failures more acute.
To ensure the integrity of our elections, we must understand overlapping vulnerabilities as a whole rather than confront them in isolation.
The Georgia primary earlier this month is a particularly severe example, when some voters waited upwards of four and five hours to cast their ballot. Long lines were caused by a pandemic-induced shortage of poll workers. A shortage of technical support workers to fix the equipment only exacerbated the problem. There were also instances where voting equipment did not function properly. (These same electronic poll books malfunctioned and caused long lines in Los Angeles County in the March primary.) On top of it all, software issues or inaccurate calibration of vote-tabulation scanners used to scan absentee ballots may have prevented thousands of mail-in ballots from being counted. Yesterday across Virginia Beach electronic poll book malfunctions created delays and required most voters to cast provisional ballots until 2:30 p.m. And problems with absentee ballots in New York meant thousands were not processed at all, and many were still being delivered Monday—dramatically increasing the likelihood thousands of voters will be disenfranchised by missing the postmark deadline yesterday.
As we have seen all year, beginning with the days-long debacle of tallying delegates for the Iowa Caucus, Georgia is not the exception but rather a particularly egregious instance of the rule for 2020 election catastrophes. It is imperative we take action now to protect the security and integrity of our elections. Over the last few years four key weaknesses have emerged in our election ecosystem: flawed infrastructure that invariably breaks, organically generated conspiracies and public outcry, vulnerability to low-cost, unattributable system hacks, and susceptibility to trolls and bots. Each of these weaknesses is problematic enough on its own, but taken together they compound the effect of one another to generate a seemingly insurmountable challenge. To ensure the integrity of our elections, we must understand the vulnerabilities as a whole rather than confront them in isolation.
• • •
Flawed Infrastructure
Election administrators will never have access to the capital and workforce necessary to fully secure an election. Core requirements of our elections, like a secret ballot and the incessant drive for immediate results, constrain election officials in ways that make security an even more elusive goal. The technology employed to administer elections is usually developed on the cheap and made for a non-technical workforce or volunteer to operate. Our elections are run with equipment that, like all technology, will invariably break.
However, the tendencies for system failure are exacerbated by dated equipment with known vulnerabilities that have gone unpatched for over a decade. Since this equipment is largely only used during the election, it is obviously most likely to break during early voting or Election Day. The examples are seemingly endless. The machines used in Texas in the 2018 midterms, those decommissioned in Georgia following the 2019 elections, and the Iowa Democratic Party (IDP) results-reporting application that broke down on Caucus Night earlier this year all contained deeply flawed software. Further, Jack Gillum of ProPublica reported in March that there were at least fifty election-related websites that were “particularly vulnerable to cyberattack.” In some cases, these websites failed to hide files that could give “a roadmap to the computer system’s weaknesses,” essentially providing an outline for hacks into these election websites. Even new voting technology has been under scrutiny. Los Angeles county has chosen a system called the Ballot Marking Device in which machines, not voters, mark choices on ballots. A study found that only 40 percent of voters double-checked their ballots and “voters missed more than 93 percent of the errors the machines introduced.” Furthermore, a new statewide California database that allowed voters to vote from any polling location failed and in some cases, this led to hours-long lines, which disenfranchised scores of voters.
An especially high-profile, yet unfortunately not atypical, instance of faulty equipment is the Iowa Democratic Party (IDP) app used on February 3—a results-reporting portal for what was arguably the most important election since 2016. Yet the IDP spent merely $60,000 to build it, and it contained essentially no security features. (For some perspective, consider that through DARPA the U.S. Department of Defense is spending over $10 million just to build a beta version of new open source, secure voting technology.) When I spoke with election security expert Harri Hursti, who studied the app, he highlighted three of the most egregious points of failure in both building and securing it:
- Software was distributed by a beta software testing platform, and the installation instructions shared by Iowa volunteers indicates that they were asked to lower their personal mobile phone security to install the app.
- The app was rapidly developed, and screenshots show the software was updated on January 24, January 30, and February 1—just days before the Iowa caucuses. This suggests normal testing and code freeze never took place. In other words, best practices to ensure quality and performance were not observed.
- Security testing should be done with the final product because every software change may open new vulnerabilities. With the software releases just days before the caucuses, claims of independent security testing are not credible because meaningful testing would have been impossible due to the schedule.
The problems get worse as we move into 2020 primaries in the wake of COVID-19. The Wisconsin primary election on April 7 is a particularly jarring example. Thousands of voters who had requested absentee ballots ahead of the deadline never received them. In Oshkosh and Appleton, for example, officials reported discovering three tubs of absentee ballots in a mail processing center after the election. In Fox Point, on the other hand, hundreds of ballots were returned undelivered, without explanation, in the week leading up to the election. Similarly, in Fox County, officials reported that a hundred or more ballots a day were returned as undelivered in the week leading up to the election. Even if completed ballots were returned, some of them were processed and sent to clerks without postmarks or were rejected because of invalid signatures.
If these same absentee ballot problems are scaled to general election level turnout totals in November, hundreds of thousands of voters could be disenfranchised in Wisconsin alone. And the Wisconsin primary is no anomaly. Similar human errors in administering absentees have been identified in the Ohio 2020 primary and Georgia and Oregon 2018 general elections. If just these examples of absentee problems caused by human error are taken together and scaled nationally, millions of voters could be disenfranchised in November. The human error will likely result from significant COVID-19 related election administration workforce shortages which predicate failure to execute the transition to near universal absentee voting.
• • •
Organically Generated Conspiracies and Public Outcry
When election infrastructure breaks, a cacophony of voices from the media and partisans on either side of the election demand answers immediately. They also demand surety in the election results and “proof” that election officials counted each vote as cast. Finally, they insist the election administrators demonstrate how winners were correctly identified—a task increasingly difficult without voter marked paper ballots. The IDP, for its part, was not able to engender trust in its results until it published all precinct tally sheets to demonstrate how they had determined the winner of the caucuses. Further, some corners of the political spectrum will instantaneously manufacture conspiracy theories about what “really” happened with infrastructure failures.
In November we should anticipate simultaneous infrastructure failures in conjunction with unstoppable, unattributable network cyber-attacks, as well as the combination of organic public outrage with bot and troll attacks promoting conspiracy theories.
This cascade of scrutiny and outcry was on full display following the Iowa Caucus. Within minutes of IDP’s troubles becoming apparent, rumors the results reporting app was hacked sprung up (something the party flatly denies). Some even began to suggest that a campaign paid for the app and rigged it. In a bizarre twist, some of the campaigns tried to suggest former Hillary Clinton staffers manipulated the app in an effort to punish the Bernie Sanders campaign. Not to be out done, even right-wing conspiracy theorists proffered their own ideas as to what dark forces pulled strings behind a veil of secrecy.
These rumors echo conspiracy theories that arose after the 2016 election. Likewise, the glitchy machines in Texas in the 2018 midterms generated conspiracy theories, as was the case with the eventually decommissioned voting machines in Georgia. The long lines in Los Angeles, California also generated conspiracy theories in the 2020 primary there. In reality, the lines were a result of several factors, including the county’s decision not to participate fully in the California Voter’s Choice Act—a new law that involves mailing every registered voter a ballot—and statewide databases failing to work properly. However, these facts did not prevent conspiracies from being generated.
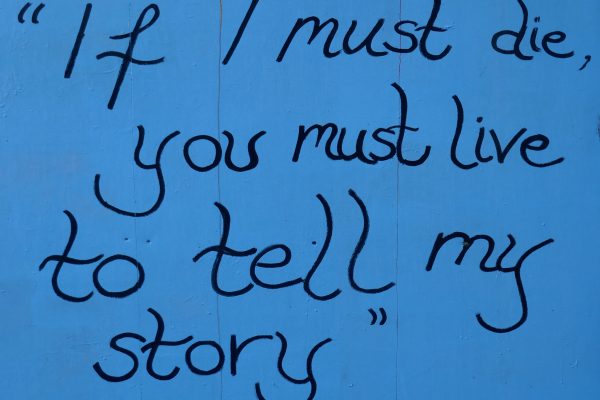
For the thousands of missing absentee ballots, the Wisconsin election officials have largely tried to hold the United States Postal Service responsible, but an investigation revealed that the infrastructure problems went far beyond just mailing issues. Additionally, with a shortage of nearly 7,000 poll workers, Wisconsin’s National Guard was called in to staff the polling sites. However, rumors began circulating that the National Guard was called in to shut down health care facilities and enforce statewide quarantines. Wisconsin voters public outcry increased after state health officials reported nineteen new COVID-19 cases linked to Wisconsin election activities. The slogan “Vote and Die” began circulating on Twitter during the primary to call attention to anxiety around voting during a pandemic.
Our own citizens can thus be counted on to generate conspiracy theories about infrastructure failures. This does not require an army of zombie Twitter bots to manufacture but only an onslaught of unrelenting traditional and social media coverage of the election infrastructure failures. Further, our own voters and journalists will organically spawn and amplify homegrown conspiracy theories. The effect of this election ecology is to breed distrust, which only further undermines the system.
• • •
Vulnerability to Low-Cost, Unattributable System Hacks
A third element that disrupts our election infrastructure are low-cost, unattributable attacks from adversaries. We already know that in 2016 Russian hackers sponsored by Main Intelligence Directorate of the General Staff of the Russian Army used the most basic of cyber-attacks, a SQL injection, to gain access to election administrators’ websites and worm their way into state and local voter registration databases. There they were able to exfiltrate data and trigger alarm bells about the election being hacked.
For the Iowa 2020 caucus, adversaries executed an even lower-tech hack using 4Chan—the largest image-based bulletin board website, with over twenty-two million visitors each month—by simply posting IDP hotline phone numbers for precinct chairs to report results on Caucus Night. These postings encouraged users of the site to jam the IDP phone lines by flooding it with calls at the same time caucus chairs were calling in results. In postings following the original message, users encouraged each other to report false precinct results. We don’t know for sure whether people heeded this call to action. However, since the lines were indeed jammed for hours, it stands to reason that some of the calls into the IDP call center on Caucus Night were from 4Chan users. Ensuring the “hack” is unattributable is in line with previous hacks.
We don’t know whether Russian attackers changed or altered voter records in 2016, just as we don't know whether 4chan users called in fake results in 2020. That uncertainty may be the point—sowing doubt about the integrity of our democratic system. In Cook County, Illinois in 2020, an unknown entity made a fake board of elections website in advance of the primary that was indistinguishable from the real one—to what end, no one knows. Further, many precincts around the country report election results into an app like the one used by the IDP. Largely unattributable attacks, like distributed denial-of-service (DDoS) attacks, could be used to ensure results can not be reported on Election Night. ElectioNet suite’s Election Night Reporting (ENR) by PCC Technology is one such web facing app used to report election results by many jurisdictions all around the country that could be vulnerable to such a low tech, unattributable attack.
• • •
Disinformation Trolls and Bots Stoke Discontent
Although, as mentioned above, the U.S. public and media generate conspiracies and public outcry on their own, online trolls and bots also serve to spread disinformation and undermine election integrity. Research conducted by the University of Chicago’s Cyber Policy Initiative immediately following the Iowa Caucus, for example, found several accounts that appeared to be bots or trolls were in fact working to amplify misinformation. Popular conservative political figures with hundreds of thousands of followers, such as Eric Trump, Rudy Giuliani, and Charlie Kirk, took to Twitter following the Iowa Caucus to push narratives that the DNC “rigged” the results. These tweets gained tens of thousands of retweets and likes. Out of the 14,900 retweets of Eric Trump’s tweets, 50 accounts are available for users to see. Of these, at least eight are likely to be bot accounts, according to BotSentinel, a machine learning and artificial intelligence system that detects fake accounts.
It has also been widely reported that bots have played a role in significant disinformation campaigns about the COVID-19 pandemic. For example, voters in Colorado have been targeted robocalls about stimulus checks and law enforcement traffic stops due to the pandemic. It is likely only a matter of time before COVID-19 becomes a key theme of election-related disinformation as we saw in the Wisconsin primary above.
Retweeting and liking tweets is more effective at amplifying disinformation due to Twitter’s algorithm. Tweets that have more engagement (re-tweets, likes, responses) are pushed to the top of users’ feeds. So bot accounts more efficiently amplify messages published by well-known media figures rather than write their own tweets in order to game Twitter’s algorithm.
• • •
Where Do We Go From Here?
All four of these vulnerabilities come together to pose a staggering threat to election security. In November we should anticipate simultaneous infrastructure failures in conjunction with unstoppable, unattributable network cyber-attacks, as well as the combination of organic public outrage with bot and troll attacks promoting conspiracy theories. COVID-19–related staffing shortfalls will only make infrastructure failures more common and severe.
Some observers, including some election officials, do not see much to worry about in these concerns. In the cases of the Iowa caucus or California primary in particular, some contend that this meddling is merely unfortunate background noise that makes life very difficult for some candidates, campaign staff, and election officials but ultimately does not affect the outcome. With such high-stakes elections, they would argue, there is bound to be some hand wringing over the vote-counting process. As long as we eventually arrive at the correct answer, does the disruption really matter?
The answer is yes. These vulnerabilities could well determine the outcome of the 2020 General Election. For one thing, voters who feel the system is rigged or compromised are likely to stay home. We must act now to ensure voters can participate in a safe, efficient and secure process where votes are counted as cast in a timely manner and the integrity of results is self-evident.
Enhancing the transparency of our election infrastructure and security measures with a publicly accessible database would dramatically enhance the security of our elections.
What exactly should be done? State and local election officials, nongovernmental organizations and federal agencies like the Department of Homeland Security (DHS) have made some progress in securing our elections. Still, we are a long way from implementing recommendations made by the National Academy of Sciences. Unfortunately, the social-cyber attacks laid out here differ categorically from singular attacks aimed at changing vote totals in a voting machine or deleting voters in a voter registration database. To be sure, voting machines and voter registration systems remain deeply vulnerable to cyber attacks—but an election official’s infrastructure is not the only thing to defend. We also must defend the perception of a secure election in the voters’ minds. This cognitive security starts with voters’ understanding these hostile campaigns are being waged against them in the first place.
First, election officials must explicitly acknowledge the risk that these social-cyber attacks will be waged on voters throughout the election season. Unfortunately, many in the election administration sector prefer not to call attention to these threats. There is a cultural norm of refusing to talk publicly about the vulnerabilities and denouncing anyone who does as exacerbating the problem. This is the wrong approach. Instead, election and national security officials must confront the risk explicitly, in part so voters can steel their mental resolve against it.
Second, election officials must be transparent in what security measures they have implemented. This includes both cyber security measures and social resilience measures like crisis communications procedures for Election Night. Many of the most cyber-mature institutions—including DHS, the Department of Defense, aerospace corporations, and banks—regularly report security measures they implement. This enables their constituents and oversight bodies to maintain a level of certainty that the security team is being held accountable. Transparency also enables stakeholders to benchmark the organization against others in their industry. We should follow their lead.
Finally, more research must be done to compile information on election infrastructure components and security measures across the country into one database available for researchers, election officials, and other stakeholders to compare jurisdictions and practices.
One model for this centralized, transparent database is the MIT Line Optimization Tool, which was designed to assess wait times for voting lines on Election Day. I co-led the team that built the earliest version of the tool on the Obama 2008 campaign. We constructed a simple algorithm that predicted wait times given basic information like how many voters were expected to vote and what type of machines were employed at a voting location. Initially many election officials opposed the tool, but as we refined it they began to see value in being armed with this knowledge, and by the 2012 Obama re-election campaign, the tool had been dramatically improved. After the election was over, the campaign released the code, and MIT hosts it today, where it is publicly available and commonly used in election administrator training. Campaigns have also used the tool to hold election administrators accountable for appropriate asset allocation.
A similar scheme could help to compile inventories of election equipment in every jurisdiction in the country. Much of this information is already public and compiled by Verified Voting and the Election Assistance Commission. Further, research should be done to compile security measures employed in each jurisdiction and benchmark those against globally recognized industry standards like the 20 Critical Cyber Security Controls. As with open-source technology, a transparent election infrastructure and security database would empower election officials to make more informed decisions. Activists and security researchers also would use the data to identify opportunities to make election infrastructure more secure. For example, during the COVID-19 crisis, this tool also could be used to track election administration workforce shortages and absentee voting challenges. Third-party volunteer experts can also help deflate conspiracy theories as they arise.
Unlike 2008, we need not rely on a presidential campaign to compile this information; much of it could be crowdsourced. Simply constructing the MIT Line Optimization Tool in 2008 was an improvement to the status quo. We had no mechanism to uniformly measure lines across the nation, much less identify choke points. The same would be true today: simply building a database and inputting some data, even if it were incomplete, would be better than the current state of affairs. As with the MIT Line Optimization Tool, the database would improve over time.
Enhancing the transparency of our election infrastructure and security measures with a publicly accessible database would dramatically enhance the security of our elections. Further, talking openly to the public about the broad threat landscape will harden their cognitive security. Both these transparency measures engender trust in our elections and give stakeholders the tools needed to enhance the security of our elections. While these measures would not fully mitigate the expanded threat landscape we face, it would dramatically enhance transparency of election administration—one positive step in what will surely be a decades-long struggle to secure our elections.