Help Us Stay Paywall-Free
Democracy depends on the free exchange of ideas. Help sustain it with a tax-deductible donation today.
Democracy depends on the free exchange of ideas. Help sustain it with a tax-deductible donation today.
Winter 2024
Political scientists Jacob S. Hacker and Paul Pierson lead a wide-ranging forum on the U.S. Democratic Party.
Fall 2023
“A curious thing has happened within American culture,” Aziz Rana writes. “The language of freedom has been claimed almost entirely by the political right.” Can it be reclaimed?
Summer 2023
What does solidarity mean, and how can movements build enough of it to change society? This issue clarifies a key idea in struggles for a more just world.
Spring 2023
Equality of opportunity is a popular ideal, but does it turn a blind eye to structural injustice? This issue explores the importance of outcomes, not just opportunities.
Winter 2023
This collection of poetry, stories, and essays engages speculation as both a ubiquitous feature of financial capitalism and a radical tool of collective imagination.
Fall 2022
Centered on movements in the Global South, this issue explores a range of radical visions for a world after neoliberalism and empire. Guest edited by Adom Getachew.
Summer 2022
Efforts to green the economy often sound like austerity measures in disguise. But what if “post-growth living” could be an opportunity for more pleasure, not less?
Spring 2022
This issue explores the meaning of law beyond the Constitution and the courts—both as a tool of oppression and as a means of collective liberation.
Winter 2022
This arts anthology explores whether and how we can repair terrible ruptures of political and social life today.
A political and literary forum, independent and nonprofit since 1975. Registered 501(c)(3) organization. Learn more about our mission
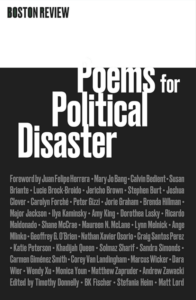
For National Poetry Month, sign up for our newsletter and get a digital copy of our out-of-print chapbook Poems for Political Disaster—with work by Jorie Graham, Ilya Kaminsky, Solmaz Sharif, Juan Felipe Herrera, and much more.
Newsletter subscribers get our latest essays, reading lists, and exclusive editorial content (plus 10% off our entire store).

For National Poetry Month, sign up for our newsletter and get a digital copy of our out-of-print chapbook Poems for Political Disaster.